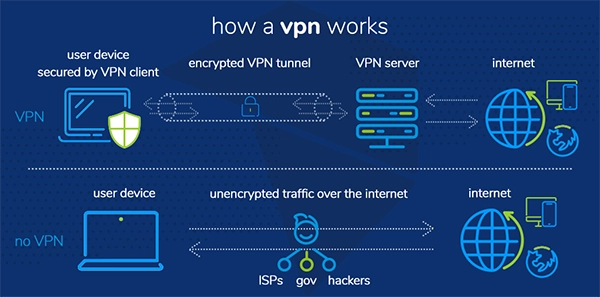
The purpose of a VPN is to provide security to a network by masking the user’s IP address and securing the network traffic by creating a “tunnel.”
How IT Consulting Services Protect Global Operations Through VPN Solutions
Global operations are securely protected by IT consulting services like IT support Mainland China. They design and manage powerful VPN solutions that secure all the data that is transferred when using unsecured public networks.
More than 70% of organisations increased VPN usage in 2024, and 81% of the remote work being done is performed using a VPN. Virtual private network solutions made specifically for businesses include tougher and longer authentication methods to provide better security.
All data sent through VPN is sent through a secure tunnel, which hides our network identity and encrypts data, making it unreadable and inaccessible to third-party individuals.
Key Takeaways
- Security is essential for modern global businesses
- VPN hides the IP address and secures network traffic
- IT consulting firms provide businesses with a lot of security measures
- International operations cannot happen without secure networks
- It is very risky to use the network for business without using a VPN
Why Secure Global Connectivity Matters for Modern Businesses

Secure global connectivity is essential for new and upcoming businesses, as there are large amounts of intellectual data that need to be kept private and secure at all times, and when that data is meant for global transfer purposes, then the stakes only increase.
Modern businesses require not only one security measure but multiple security procedures to counter various global threats and third-party individuals looking to gain access to restricted data and cause major harm to the business.
Hence, it is essential for firms to make use of Virtual Private Network (VPN) solutions as a strong safety measure that protects the company from incurring major losses.
Understanding the Role of VPNs in Business Security
Cybersecurity is the modern need of the hour for every successful business; it has become an essential part of every firm’s work, as it introduces many security measures to combat malicious attempts on a company’s data.
One such cybersecurity method is the usage of a VPN software or solution. A VPN essentially secures all flowing data through an unsecured public network by masking the user’s IP address and using cryptographic methods on the data to make it secure and unreadable by any unauthorized party trying to gain access to it.
How IT Consulting Services Implement VPN Security Strategies
The implementation is a technically complex procedure in which many steps are taken, such as :
- Designing and Assessment – The auditing of pre-existing complex structures are done by consultants to find weaknesses or vulnerabilities. This involves risk analysis, identifying the needs of the business according to the budget, and selecting secure and modern protocols.
- Multi-factor Authentication (MFA) – Using two-factor authentication for accessing data, implementing the use of biometric access rather than being passcode-centric to prevent credential theft. Digital certificates, which are hidden and attached to every file, verify whether it’s authentic or not. These are added as a security measure to better the security.
- Access Control – Hackers are prevented by limiting what a user sees when connected to a network. Zero Trust protocols are applied in which only minimum and necessary permissions are given to a person based on the requirements of their role, additionally dividing the network into different segments proves to increase security by a huge margin.
- Maintenance – Regular security updates to software are a necessary task to uphold, as every day a new type of threat is discovered, so our software needs to be updated to counter them at any time. Also, extra features that are not used can be disabled until fixed to fix an urgent security breach.
- Regular Monitoring – Frequent logging and monitoring of the network and its record of traffic needs to be monitored so that no unusual or suspicious behaviour goes by without raising an alarm.
- Compliance by Standards – VPNs need to follow laws set by the government and should comply with the set standards of quality before they get released. Performance optimization is most important as VPNs should not slow down other processes of the business while working.
Fun FactAsia, Africa, and the Middle East have the highest adoption of VPNs, with over 35% users using VPNs on their devices.
Protecting Remote Teams and International Operations
Many technical roles allow remote work, where employees do not need to be physically present in one place. As the teams are more geographically dispersed, more global operations take priority.
To protect the business from outside threats that may seek to harm and disrupt the business processes of the firm, we need to have a good and strong cybersecurity place, which involves using a virtual private network (VPN).
IT consulting firms are contacted for this sole reason, as they specialise and have expertise in these matters and can reduce the risk of data losses and theft.
Common Security Risks Without VPN Implementation
If a business doesn’t opt to go with VPN implementation, then these are the major security risks that may harm their entire system :
- Exposure to Public Wi-Fi – Connecting to an unverified public wifi without the use of a VPN could cause major damage as our data and information can be accessed and used at any time, as it is not protected or hidden from anyone.
- Risk of Malware and Viruses – Not running a VPN while transferring data or information through the internet can lead to contracting malware or viruses, which makes our system and data prone to deletion, contracting ransomware or even complete loss of our intellectual property to viruses.
- MITM Attacks – When connected to a network, a third party may see our data and use it for malicious purposes, which is known as Man in the Middle Attacks (MITM).
- Remote Access Compromization – When we connect to a company server without a VPN, we expose our business data to unauthorized and brute force attacks.
- Location Exposure – A VPN masks the IP address, thus hiding our location. If that’s inactive, then the geo location of the company can be targeted, leading to internet blocks which compromise our IP address and access to systems.
Conclusion
Every business needs a proper cybersecurity response team and its own reliable VPN service, which is why IT consulting firms need to be approached when these types of requirements are needed, as they have the expertise to help provide safe and reliable solutions for the firm and secure its information, location, and sensitive data from the world.
FAQs
What is the purpose of a VPN?
Why is Cybersecurity needed for a business?
Cybersecurity is essential for a business as it helps with the protection and encryption of the company’s data and documents, while also keeping threats out of the system.
What are online security risks?
Virus, Malware, Man in the middle (MITM) attack, Ransomware, Location Exposure are some of the online security risks that can cause harm to your network.
Does a VPN change my location virtually?
Yes, a VPN can change your location virtually, for example. If you are from the United States and connect to a VPN and choose a region in Asia, then the VPN will tunnel your virtual location to Asia.


