When applied to high-risk areas, code audit services are best at uncovering logic flaws, insecure update mechanisms, and business-logic abuse paths that SBOM tooling doesn’t detect. SBOM tooling excels at inventory and known-CVE tracking. Both address different layers and work best together.
Reducing Supply Chain Risks Through Secure Software Development

“An ounce of prevention is worth a pound of cure.”
— Benjamin Franklin (Founding Father of the USA)
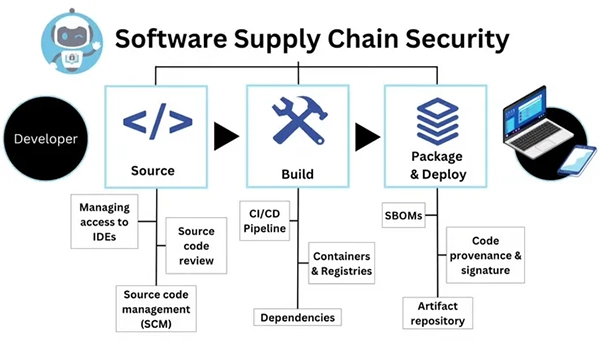
Software ecosystem attacks have quietly outgrown the perimeter most teams still defend. They now seep into build pipelines, developer machines, and third-party components long before production is even in play. What used to be a narrow security problem has turned into a sprawling, system-wide risk.
This guide lays out a practical, end-to-end approach: secure-by-design development, meaningful code audits, hardened CI/CD, signed artifacts, and visibility tools like SBOM and VEX. These aren’t theoretical controls; they’re the kind you can start applying this quarter.
A quick reality check: 13% of Log4j downloads are still vulnerable versions. That’s not cutting-edge exploitation; that’s attackers winning through patience. Long-tail exposure is where many teams lose.
KEY TAKEAWAYS
- Supply chain attacks now target pipelines, dependencies, and developer environments, not just production systems.
- Secure-by-default practices and policy-as-code are more effective than manual enforcement.
- Code audits uncover deeper risks that automated tools often miss.
- Dependency hygiene and SBOM visibility are essential for long-term risk reduction.
Supply Chain Risk Exposure Map Across the Secure SDLC
Understanding risk stage-by-stage is the difference between targeted defense and scattered effort.
Not every stage of the SDLC carries the same ecosystem risk profile. Treating them as equals can lead to misaligned controls, security gaps, and missed exposure at the moments that matter most. Mapping risk across the Secure SDLC helps teams apply the right safeguards at the right stages. You can also hire professional code audit services for software security for the job. It uncovers hidden risks early, so controls reduce real exposure, not just add process.
Risk Hotspots by Stage
Design phase weaknesses are structural. Missing trust boundaries and insecure architecture decisions create problems that no downstream patch fully resolves.
Move into coding, and you’re introducing vulnerable commits, unsafe dependency choices, things that automated scanners routinely underreport. Build and release phases carry their own distinct threats: poisoned CI runners, unsigned artifacts, and missing provenance chains.
These aren’t hypothetical concerns; they’ve driven some of the most high-profile incidents of the last several years.
Attack Surfaces that Many Teams Miss
Shared CI/CD runners. Private artifact registries. Developer workstations. These are consistently underprotected, often because nobody formally owns them from a security perspective. Secrets spread across pipelines, build outputs, and logs create persistent exposure. Transitive dependencies, the libraries your libraries depend on, frequently run completely unsupervised.
Fast Triage Model to Prioritize Investment
Score risks through the lens of impact × likelihood × blast radius. Map your crown jewels: signing keys, build infrastructure, source repositories, production deploy paths. Identify single points of failure, a single CI provider, one registry, and one critical SaaS vendor, because concentration risk amplifies exposure faster than most teams realize.
With that picture in front of you, the next step is turning awareness into engineering controls that hold up under real-world pressure.
Secure Development Controls That Directly Reduce Supply Chain Risk
Security controls only work if developers actually follow them. Controls developers routinely bypass don’t reduce risk, they produce compliance theater and a false sense of security.
Governance That Engineering Will Actually Follow
Define ownership clearly across Product Security, Platform, and Dev leads. Encode dependency lifecycle controls as policy-as-code: dependency gates, merge rules, signing checks. Build workflows where audit artifacts emerge naturally from normal release processes, not as a last-minute scramble before a review.
Secure-by-Default Engineering Guardrails
Standardize secure templates for repos, pipelines, and IaC modules. MFA, branch protection, and least privilege are non-negotiable baselines, not optional enhancements. Treat security requirements as acceptance criteria for releases, not reactive responses to incidents.
Developer Enablement That Prevents Insecure Patterns
Stack-specific secure coding playbooks, Java, Node, Python, and Go, give developers actionable guidance exactly when they need it. Safe wrappers for crypto, auth, and deserialization reduce subtle, hard-to-catch errors at the source. Contextual PR prompts surface relevant security signals without turning every single commit into a friction event.
Guardrails set the right boundaries. But they don’t catch what’s already written into your codebase, and that’s exactly where targeted code audits become your sharpest upstream dependency defense.
Code Security Audits and Source Code Review as Supply Chain Risk Controls
Automated tools are helpful, but they don’t see everything. Business-logic abuse paths, multi-tenant isolation gaps, signature verification flaws- these don’t surface cleanly in SAST output. That’s where secure code review services deliver depth and context that tooling alone genuinely cannot match.
The following infographic depicts this clearly:
Code-Level Risks That Translate Into Supply Chain Incidents
Unsafe update mechanisms, insecure plugin architectures, and dynamic code loading are particularly dangerous in a dependency-driven environment. Custom installers and dependency management logic often contain logic flaws that create silent compromise paths nobody noticed during initial development.
Build-time behaviors in postinstall hooks and pipeline scripts deserve the same rigorous scrutiny as your core application code.
Audit Scope That Actually Reduces Blast Radius
Prioritize critical modules:
- Authentication systems
- Update and patching logic
- Config management
- cryptography implementations
- CI scripts
Treat Dockerfiles, Helm charts, and Terraform as first-class code, not infrastructure afterthoughts. Dependency review and license posture belong in the audit plan from day one.
Deliverables That Make Audits Actionable
Risk-ranked findings paired with realistic exploit scenarios and specific fix patterns move remediation faster than raw vulnerability lists ever can. Mapping findings to SSDF and SLSA controls gives stakeholders a concrete framework. Remediation verification, retests, regression tests, targeted guidance, closes the loop, and builds the defensible evidence trail your organization needs.
Even the most thorough code security audits only cover code your team controls. The dependencies running quietly underneath deserve equally rigorous attention.
Dependency Hygiene That Prevents “Invisible” Compromise
Dependencies are convenient, but they’re also one of the easiest ways in for attackers.
CISA’s 2024 guidance found that 85% of audited codebases contained open-source software not updated by developers in more than four years. That’s not a fringe problem. It’s structural.
Dependency Intake Rules That Reduce Risk Without Blocking Delivery
Evaluate maintainability before adopting a new package: release cadence, contributor diversity, and maintainer provenance all matter more than you might think. Prefer fewer dependencies. Avoid single-function libraries when existing components already meet the need. Use lockfiles, controlled upgrades, and reproducible installs to prevent silent drift between environments.
Build-Time Dependency Attack Prevention
Private mirrors and registry allowlists block dependency confusion and typosquatting attacks before they ever reach your build environment. Enforce hash verification and provenance checks at intake. Any dependency without a verifiable integrity signal should be treated as untrusted by default, no exceptions.
Locking down dependency intake is essential. But you also need a clear, real-time record of everything that actually made it into your software. That’s what a well-implemented SBOM and VEX strategy delivers.
SBOM + VEX, Provenance, and CI/CD Hardening
Think of these as visibility, context, and proof working together.
SBOM Practices That Create Operational Value
Generate an SBOM per build and store it alongside the artifact. Include containers, base images, OS packages, and build tools, not just application-level dependencies. Build in a versioning and retention strategy, so you have what you need when an incident response situation demands it.
CI/CD Pipeline Hardening That Blocks Intrusions
Least-privilege service accounts with short-lived tokens limit the blast radius of a compromised runner significantly. Separate build, test, release, and deploy roles so no single identity can push code from commit straight through to production.
Golden pipelines with centralized policy enforcement, dependency gates, signing checks, and merge rules; scale these controls across every team without requiring manual configuration each time.
Containing threats at runtime matters enormously, but sustaining organizational investment requires connecting all of these controls to measurable outcomes that demonstrate genuinely reduced risk.
Metrics and Implementation Roadmap
Security improves when it’s measurable.
KPIs That Connect Secure Development to Supply Chain Outcomes
Track the mean time to identify impacted systems from a new CVE. Track the mean time to remediate by severity and exposure level. Track the percentage of releases shipping with SBOM, provenance, and signatures attached. Dependency freshness rates and unsupported component percentages round out a dashboard that executives can actually understand and act on.
Implementation Roadmap: 30 / 60 / 90 Days
First 30 days: inventory critical apps and pipeline paths, implement branch protection and CI hardening fundamentals, start SBOM generation for top products, and initiate a targeted source code audit focused on modules carrying the highest security impact.
Days 31–60: add signing and verification gates in deploy workflows, enforce a dependency intake policy with a private proxy, and formalize vendor transparency requests, SBOM, VEX, and SDLC evidence documentation.
Days 61–90: standardize provenance and attestation across the organization, expand golden pipelines, add runtime verification layers, and schedule recurring secure code review services aligned to major releases and meaningful architectural changes.
Securing Your Software Supply Chain
Risk isn’t a future problem waiting to arrive; it’s already woven into how modern software is built.
The controls outlined here aren’t aspirational frameworks. They’re practical, implementable steps that engineering teams at every maturity level can begin executing within weeks.
From SBOM generation to CI/CD hardening, from dependency governance to recurring code audits, the path forward is concrete. Start with your highest-risk modules. Build outward from there. Every release cycle you delay, the cost of inaction compounds.
FAQs
Which ecosystem risks are reduced most by code audit services versus SBOM tooling?
When should teams choose secure code review services instead of, or in addition to, SAST/DAST?
Secure code review services add value when SAST generates high false-positive rates, when business logic is complex, or when the codebase handles authentication, cryptography, or update mechanisms, areas where human analysis catches what automated tools routinely miss.
Which parts of a CI/CD pipeline should be included in a source code audit?
A source code audit should cover pipeline configuration files, build scripts, Dockerfiles, Helm charts, post-install hooks, secret handling, and any script that executes during build or deploy, not just application source code.