Ans: Slow internet speed due to distant servers or heavy usage, limited access on some websites and platforms, are a few drawbacks of VPN tunneling.
What is a VPN Tunnel? How Does it Work and Different Types Explained?
VPN Tunnel is a term you may not have heard, but you’ve surely used whenever you connect to a VPN.
It is the mechanism in the VPN that protects your generated data and other online activities from internet snoopers, providing you with a safer online experience.
But how does it really work? What are its other benefits? Are there any types of VPN tunnels? Let’s find out in this all-encompassing write-up on what is a VPN tunnel.
What is a VPN Tunnel and How does it Works?
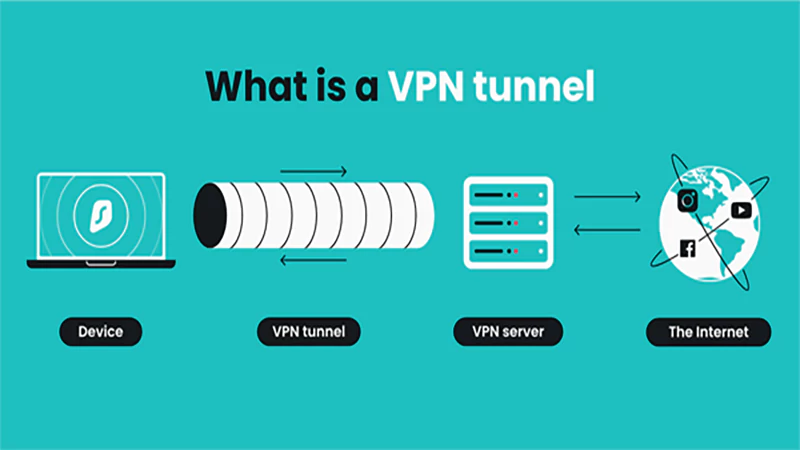
A VPN tunnel is a process of creating a tunnel (an encrypted connection) that
masks the IP address, encrypts data, and ensures that the generated data travels safely between your device and the VPN server.
Think of it as the protected, sealed tunnel through which VPN is transporting valuables (your data) without compromising the security and privacy of your personal and confidential data.
It deceives the online hackers, or say meddlers, by converting the respective connection into an unreadable code that can not be deciphered.
But how is it different from VPN? As we mentioned above, it is a robust pathway of all the fastest VPNs, such as Vpneer, that makes sure your data travels smoothly, ensuring high privacy and security of the information.
How Does it Work?
A VPN tunnel uses different tunneling protocols to establish a strong, secure connection between your phone or PC.
Then it routes your data or internet traffic through this tunnel that safeguards your information from any kind of unwarranted interference.
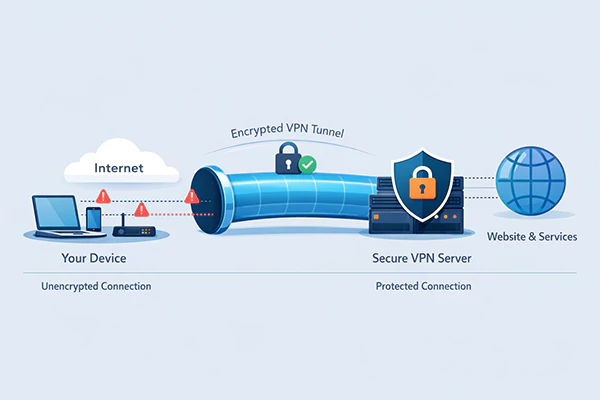
Here’s an illustration that will help you understand how a VPN tunnel works:
Types of VPN Tunneling Protocols
Primarily, these are six types of VPN tunneling protocols used by VPN service providers. Check them out below:
| Tunneling Protocols | Description | Security | Speed |
| WireGuard | Open-source, lightweight, transparent, easy to customize, and debug. | Excellent | Excellent |
| OpenVPN | Open-source, downloadable, and modifiable, it can run over TCP or UDP internet protocols. | Good | Good |
| IKEv2/IPSec | Provides security perks of IPSec and speed of IKEv2, with incompatibility issues with some platforms. | Good | Good |
| L2TP/IPSEC | Accepts varied encryption protocols, easily customizable, plethora of documentation available, outdated, and struggles to bypass firewalls | Average | Average |
| SSTP | Easy-to-set-up, accessible support, compatible only with Windows OS. | Good | Average |
| PPTP | Fast, convenient, compatible with every system, easy-to-set-up and use, outdated protocol, easily blocked by firewalls. | Poor | Good |
These tunneling protocols are distinct from each other in terms of speed, security, encryption processes, and other features. Now, let’s shed light on the benefits of VPN tunneling.
What are the Benefits of VPN Tunneling?
By now, we already know that a VPN tunnel prevents your data from any form of interception and provides a robust end-to-end secured connection.
So, here are some other overarching benefits of a VPN tunnel:
- VPN tunnels make sure that no one can track your activity online, resulting in no bandwidth throttling by ISPs, as it slows down your connections based on your internet activity.
- It fosters remote working (key feature of Remote Access VPN) by allowing you to access your organization’s internal systems or files more securely and conveniently with the help of a VPN concentrator.
- VPN tunneling also ensures that third-party sites can’t accumulate your data for ads and targeted campaigns.
- It provides an extra layer of protection when connected to open networks such as cafes, hotels, airports, libraries, etc. Your message, login credentials, and other personal information are completely safe.
To experience and enjoy the advantages of a VPN tunnel, you have to connect to a VPN, and your connection is formed even if you’re connected to an open network.
What is VPN Split Tunneling? Explained!
As the term suggests, VPN Split tunneling lets you split your internet traffic, allowing you to route only selected apps or websites.
In other words, it gives you the option to choose a connection for your different parts of your online activity. You can choose a secure VPN tunnel for certain internet activities and a regular internet connection for normal browsing.
The best usage of VPN Split tunneling is that you can use it for sensitive online activities, such as online banking, while disabling other traffic for faster speed during streaming, and other routine surfing.
To enjoy this feature, you can attempt to enable it through your device or contact your VPN service provider to unlock it or opt for a new vpn service that provides both: the best VPN service for streaming and sensitive online activities.
But are there any cons to it? Let’s find out in the pros & cons section.
VPN Split Tunneling Pros & Cons
| Pros | Cons |
| Provides customizable connection options for different internet traffic parts. | Outside routed traffic is exposed to the ISP, third party, and anyone who is tracking your activity. |
| Routes only selected apps or websites’ traffic through the VPN. | If malware gets into your device system through the unsecured network, it could compromise the apps routed through the tunnel. |
| Ideal for sensitive online activities such as online banking, remote working, etc. | Prone to hacking, data theft, and malicious tracking and other interceptions on the open networks, |
| Offers better speed for insensitive traffic like streaming. |
Now that you know VPN tunnel, how it works, its types, advantages, and VPN Split tunneling, including its pros & cons. Let’s understand how you can recognize whether a VPN tunnel is established or not.
How to Identify a VPN Tunnel is Working Correctly?
It is profound to identify whether a VPN tunnel is established or not, to understand that your internet traffic is encrypted and traveling through the tunnel securely.
So, here are a few best practices that you can take into account to know that your VPN tunnel is established and acting right:
- Changed IP Address: If your IP address is changed to the one VPN provided, it proves that your device is linked to the server. You can check this by visiting an IP-checking website before and after connecting to a VPN.
Note: By using this practice, you only determine the connectivity to the server, not that your data is being secured through a VPN Tunnel.
- DNS Leak Test: If your DNS leak test result shows that the DNS requests are still traveling through your ISP, not through the VPN’s DNS servers, it simply means that some parts are not transmitting the traffic via the VPN Tunnel.
- Third-Party Network Monitoring Software: Network Monitoring Softwares are another effective way to recognize that your online activities are encrypted through a secure VPN tunnel or not. It provides a comprehensive picture that showcases whether your data is secured or at risk.
Conclusion
VPN Tunnel is an integral element of a VPN that promises a secure, encrypted end-to-end connection (a tunnel) between your device and VPN server by using different VPN tunneling protocols.
It is the mechanism that protects your generated data from any eavesdropping and interception.
Therefore, it becomes utmost important to choose a VPN service that leverages advanced VPN tunneling protocols to provide a smooth and protected online experience.
Vpn Tunneling Related FAQs (Frequently Asked Questions)
Q: What are the disadvantages of a VPN Tunnel?
Q: Can someone hack a VPN tunnel?
Ans: Yes, a VPN tunnel can be hacked only if the VPN service provider uses fragile encryption, outdated tunneling protocols, or is compromised itself. Although it is rare and taxing to track a VPN tunnel.
Q: How to choose the right VPN service provider?
Ans: Here are the things that you should take into account when seeking a reliable and cheap VPN service provider:
- Secure and Modern Tunneling Protocols (OpenVPN, Wireguard)
- Fast VPN Serves with High-Speed Protocols
- All Device Accessibility and Platform Compatibility.
- Strong Security Package (Data Encryption, Secure Authentication, Kill Switch, DNS Leak Protection, Split Tunneling Options, and Cyber Threat Protection Features)
- Wide Server Coverage
- Responsive Customer Support
Sources: